A Medium post published over the weekend claims to have discovered a vulnerability in ETH ERC-20 contracts, which the author states affects “more than a dozen ERC-20 contracts.”
According to the post, the exploit is done through a “batchOverflow” a “classic integer overflow” issue, which occurs when computers deal with numeric values outside of the range that can be represented with a given number of bits.
The post includes a proof-of-concept, which appears to show the researchers generating a nearly unlimited amount of tokens from a vulnerable ERC20 token contract.
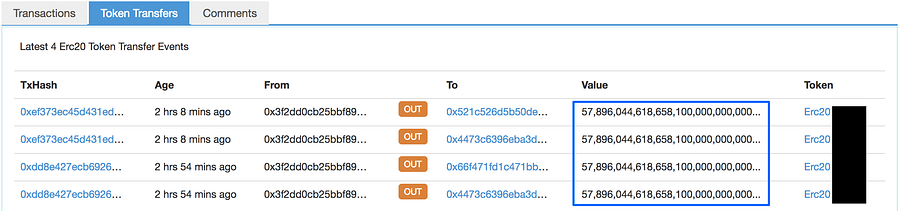
Another similar bug deemed “proxyOverflow” was also discovered yesterday by Blockchain security startup PeckShield which observed a suspiciously large amount of MESH tokens being transferred.
The researchers noted that their study found that the bug is present in a number of tokens, including – UGToken, SMART, MTC, FirstCoin, GG Token, CNY Token, MESH and SMT tokens. While others still may be affected by the bug.
“A proper way to recover from these vulnerabilities and devastating effects requires coordination and support from all eco-system members, especially digital asset exchanges,” PeckShield wrote. “In the meantime, we cannot over-emphasize the importance of performing a thorough and comprehensive audit of smart contracts before deployment.”
ERC-20 tokens make up about 90 percent of the $53 billion token market, according to data by CoinMarketCap. In response, at least two exchanges, Poloniex and OKEx, temporarily suspended ERC20 token deposits. The service is back up on Poloniex.
In a statement published Tuesday, the Hong Kong-based exchange OKEx— third-largest in the world as measured by daily trading volume — announced the suspension of deposits, explaining that attackers have exploited a smart contract bug called “batchOverflow” to generate “an extremely large amount of tokens” seemingly out of thin air and then deposit them into a normal Ethereum address.
“We are suspending the deposits of all ERC-20 tokens due to the discovery of a new smart contract bug – ‘BatchOverFlow’. By exploiting the bug, attackers can generate an extremely large amount of tokens, and deposit them into a normal address. This makes many of the ERC-20 tokens vulnerable to price manipulations of the attackers,” OKEx wrote.
“To protect public interest, we have decided to suspend the deposits of all ERC-20 tokens until the bug is fixed. Also, we have contacted the affected token teams to conduct investigation and take necessary measures to prevent the attack,” the exchange added.
Changelly, a cryptocurrency trading service that acts as a broker between users and exchanges, has also suspended ERC20 token trading in response to the exploit.
Dear Customers, ERC20 tokens are temporarily unavailable due to an exploit check. We will bring them back, once we are sure there is no vulnerability in deposits received. Follow the updates! https://t.co/qYutri4X3X
— Changelly.com (@Changelly_team) April 25, 2018
This comes a day after some users of MyEtherWallet, an app for storing and sending Ether and Ethereum-based tokens, suffered a DNS hijack attack that resulted in theft of some users’ funds from the interface for the ETH blockchain.
Ethereum is currently trading at [FIAT: $647.60] down -8.19% while Bitcoin is trading at [FIAT: $9,159.44] according to Coin Market Cap at the time of this report.
